Update: Microsoft Defender for Endpoint mobile threat defense capabilities for iOS are in public preview as of October 1, 2020.
We are excited to share with you the next steps in our journey to deliver industry leading endpoint security capabilities across all platforms. Rob Lefferts, Corporate Vice President, Microsoft 365 Security and Compliance, shared our commitment to build solutions that enable a single view of your entire estate.
With Microsoft Defender for Endpoint, that is exactly what we set out to do when we announced just a year ago that we are extending endpoint security beyond Windows to Mac, Linux, Android, and iOS. With Microsoft Defender for Endpoint, now available on all the major platforms, security teams benefit from having a single, unified view of alerts, events, and threat insights, giving them visibility across all endpoints their employees are using to get their jobs done. These capabilities come at a critical time, when many workers are accessing corporate data outside of the office and on their personal devices, making it more difficult for security teams to have the visibility they need.
Our customers have joined us on this evolution and given us feedback in every step of the way. For this, we are truly grateful and look forward to the continued partnership.

Delivering on mobile threat defense
As of today, Microsoft Defender for Endpoint on Android is generally available, delivering the rich set of capabilities we announced in public preview, which include phishing and web protection, malware scanning, and additional breach prevention through integration with Microsoft Endpoint Manager and Conditional Access. These capabilities offer protection against some of the most sophisticated malware threats we’ve seen on the platform.
Since our public preview announcement, we have also updated how users can get the Microsoft Defender for Endpoint app on their Android devices. Now, eligible users can download Microsoft Defender for Endpoint from Google Play.
For additional information on how to get started, check out the documentation.
The threat landscape on mobile is truly unique. The biggest threat on mobile devices is phishing attacks, where the majority of these happen outside of the bounds of email, in places like messaging apps, SMS, phishing websites, and other apps. What makes these threats even more challenging is the nature of user interaction with mobile devices. Smaller screens coupled with touch input and gestures create the ideal situation for a user to accidentally touch, scroll, or click on something that might be malicious. It’s much harder to see if there’s an overlay on the screen, or the full URL of a potential phishing site. Users can’t check if links are malicious, like they easily can on a desktop. The inherent characteristics of mobile devices are what make it much easier for anyone to fall victim to a phishing attack.
Phishing is where we believe we bring the strength of the Microsoft security platform to bear. The scale of our service gives us extensive visibility into the billions of phishing attacks and social engineering techniques our customers face and enables us to detect and prevent these attacks on mobile.
Mobile threat defense for iOS
Given the considerable challenges of phishing on mobile, we have invested in extending phishing and web protection to iOS as well. We’re excited to share that in the coming weeks, Microsoft Defender for Endpoint will be arriving in public preview for iOS.
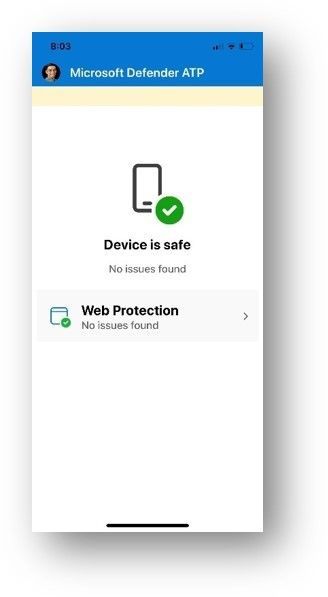
For devices running iOS 11.0 and higher, Microsoft Defender for Endpoint offers:
-
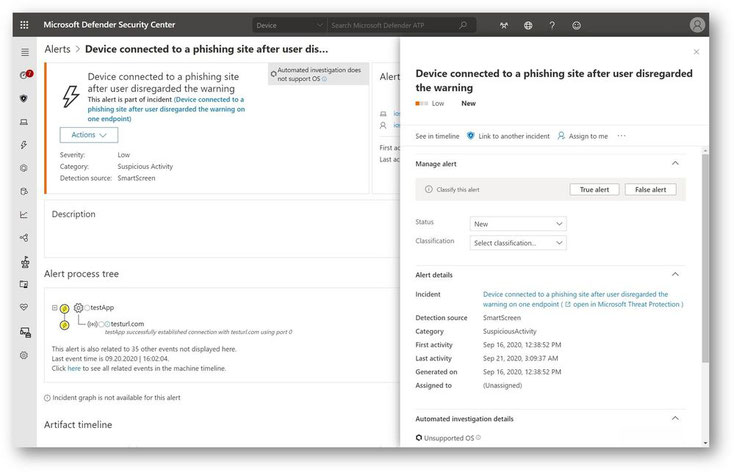
Anti-phishing: Access to unsafe websites from SMS/text, WhatsApp, email, browsers, and other apps is instantly blocked. To do this, we leverage the Microsoft
Defender SmartScreen service to help determine whether a URL is potentially malicious. If access to a malicious site is blocked, the device user gets a notification about this with the
options to allow the connection, report it safe, or dismiss the notification. Security teams are notified about attempts to access malicious sites via an alert in the Microsoft Defender
Security Center.
-
Blocking unsafe connections: The same Microsoft Defender SmartScreen technology is used to also block unsafe network connections that apps automatically might make
on the user’s behalf without them knowing. Just as in the phishing example, the user is immediately informed that this activity is blocked and is given the same choices to allow it, report it
as unsafe, or dismiss the notification. When these connections are attempted on a user’s device, security teams are notified of this via an alert in the Microsoft Defender Security
Center.
- Custom indicators: Security teams can create custom indicators, giving them more fine-grained control over allowing and blocking URLs and domains users connect to from their iOS devices. This can be done in the Microsoft Defender Security Center and is an extension of our custom indicators capability already available for Windows.
Security teams will get the same unified SecOps experience in Microsoft Defender Security Center as they get with all the other platforms – offering them a true single pane of glass view of alerts and threats across endpoints, no matter what the OS.
For more information, including system requirements, prerequisites, deployment, and configuration instructions visit our documentation.
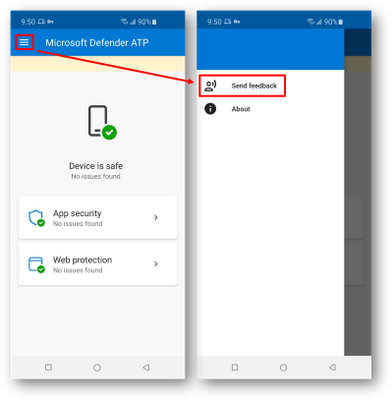
In both apps, on Android and iOS, to share feedback, you can use the “send feedback” option:
Advancing our solution for Mac
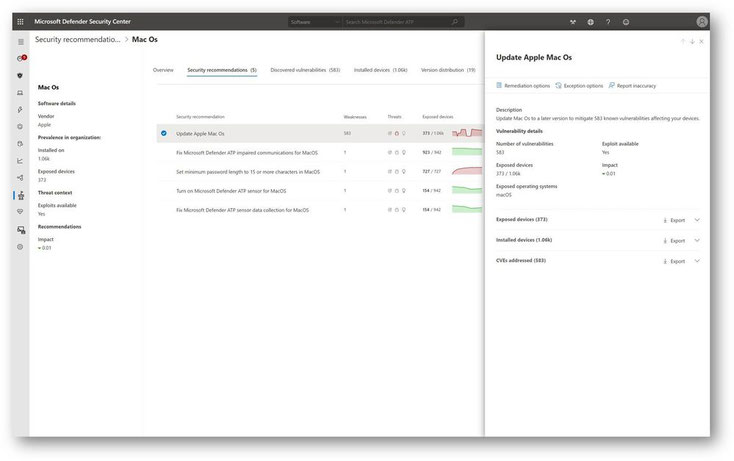
Extending our endpoint security capabilities to macOS was the first step in our journey. Today, we are thrilled to announce our next milestone! Threat and vulnerability management for macOS will go into public preview this week, expanding your visibility into vulnerabilities across your environment and providing a more comprehensive view of organizational risks. Effectively identifying, assessing, and remediating endpoint weaknesses is critical in running a healthy security program and reducing organizational risk. Threat and vulnerability management serves as a solution for reducing organizational exposure, hardening endpoint surface area, and increasing organizational resilience. Threat and vulnerability management for macOS will continuously detect vulnerabilities on your macOS devices and will help you prioritize remediation by focusing on risk, which reflects Microsoft's threat intelligence, and accounts for severity, criticality, and business value of an asset in addition to being threat aware.
In the Microsoft Defender Security Center, customers will be able to see macOS included in the software inventory and security recommendations. Just like with other software, security teams will get information about macOS specific Common Vulnerabilities and Exposures (CVEs) along with their level of severity and how many devices are exposed in their environment.
Once vulnerabilities have been discovered and prioritized based on risk, security teams can either remediate them or create an exception to indicate that remediation is planned, or remediation through a third-party control is being employed. If they choose to remediate, threat and vulnerability management enables simple and effective collaboration with IT. Security teams can open a remediation ticket directly in Microsoft Intune for Azure Active Directory joined devices and set a priority and due date for the action. As the IT team works to remediate the vulnerability, the security team can monitor real-time progress within the Remediation dashboard which gives visibility into all remediation activities in progress. Using data filters, teams can analyze remediations by activity, the related component, priority level, status, etc. These views can be exported for reporting.
Register now
We’re excited for you to see what’s next on macOS and look forward to deliver improvements to the experience such as our recent move to system extensions in preparation for macOS 11 Big Sur as well as a simplified deployment and configuration experience through Microsoft Endpoint Manager.
We've recorded a few sessions for you to learn more about our cross-platform expansion and threat and vulnerability management. Get the latest updates, see some demos, and a get a preview of our roadmaps in these sessions:
- For additional details and demos on our cross-platform capabilities, watch our recorded session: How Microsoft Defender for Endpoint protects your non-Windows endpoints.
- For a deeper dive into the latest on threat and vulnerability management, watch our recorded session: Modernize risk management with the latest threat and vulnerability management capabilities.
To get started with Microsoft Defender for Endpoint public preview capabilities, we encourage customers to turn on preview features in Microsoft Defender Security Center.
Licensing requirements
With the extension of endpoint security capabilities across these various platforms, we wanted to give you an update on how Microsoft Defender for Endpoint is licensed.
Eligible Licensed Users may use Microsoft Defender for Endpoint on up to five concurrent devices. Microsoft Defender for Endpoint is also available for purchase from a Cloud Solution Provider (CSP).
- Customers can obtain Microsoft Defender for Endpoint on Mac through a standalone Microsoft Defender for Endpoint license, as part of Microsoft 365 A5/E5, or Microsoft 365 Security.
- Recently announced capabilities of Microsoft Defender for Endpoint on Android and iOS are included in the above mentioned offers as part of the five qualified devices for eligible licensed users.
- Microsoft Defender for Endpoint on Linux is available through the Microsoft Defender for Endpoint (Server) SKU that is available for both commercial and education customers.
Please contact your account team or CSP for pricing and additional eligibility requirements.
If you’re not yet taking advantage of Microsoft’s industry leading security optics and detection capabilities for endpoints, sign up for a free trial of Microsoft Defender for Endpoint today.
Contact
Source: https://techcommunity.microsoft.com